The only aim in Rust is to survive. Everything wants you to die - the island’s wildlife and other inhabitants, the environment, other survivors. Do whatever it takes to last another night.

So many changes! We've updated Harbor/Cargo, Oilrig, Bradley, Electricity, & Patrol Heli. Adding our first Retro TC Skin & a minigun, plus much more!
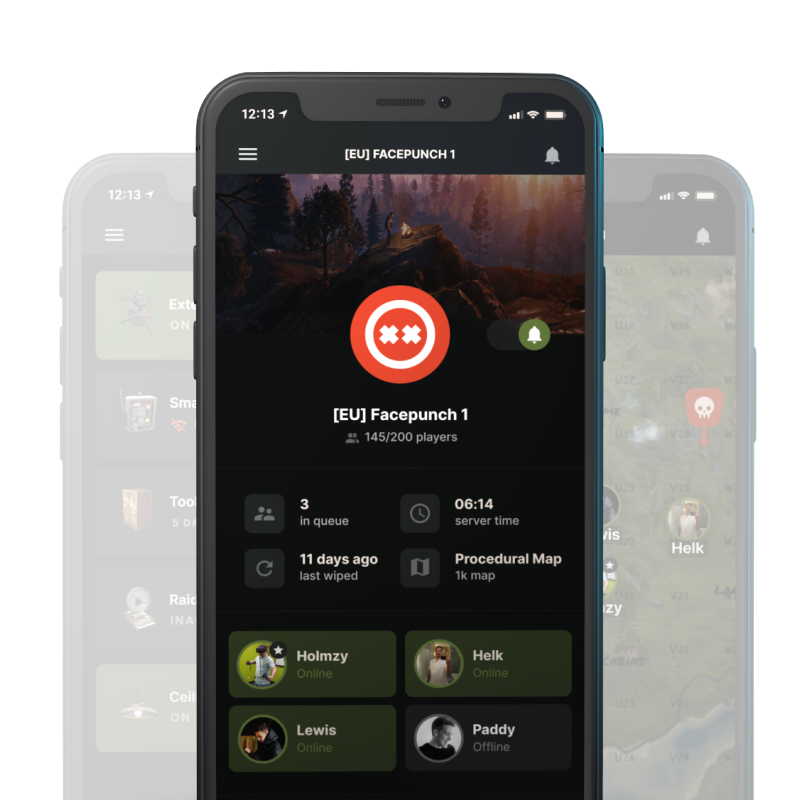
Read moreThe official Rust companion app – stay connected to the game so you never miss an important moment again. Coordinate with your team, receive alerts when you’re being raided, remotely set off traps, and more!
Learn More